Playing With s3 Leaks
Hi Everyone,
My name is Aswin Thambi Panikulangara (R0074G3N7). In this writeup, I will be sharing my technique of enumerating s3 buckets, finding misconfigurations, and recent bug I found in a public program(P1).
Tools : Subfinder, Ffuf, waybackurls
*.redacted.com is in scope. As usual, I started with subdomain enumeration, for subdomain enumeration I usually use subfinder.
subfinder -d redacted.com > subdomains.txt
Now I used ffuf for Fuzzing and enumerating s3 buckets.
ffuf -u http://FUZZ.s3.amazonaws.com -w subdomains.txt
After fuzzing got 5 buckets. Four of them were denied access and one was open.
Bucket was like : sub.redacted.com.s3.amazonaws.com
So I need to confirm this bucket belongs to redacted.com. I used waybackurls this time.
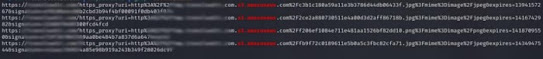
cat subdomains.txt | waybackurls | grep s3.amazonaws
After seeing this just tried to list the bucket.
aws s3 ls s3://sub.redacted.com
Bucket listed successfully!!!
It was leaking tons of private pictures of users where anyone can access it publicly.
Again I tried to mv, cp files into the bucket but failed. So reported this directly to the company.
2021 July 29 reported.
2021 July 29 triaged as critical, fixed.
2021 July 30 listed in HOF page.
2021 July 30 rewarded with Swags.
THANKS.
follow me on twitter: https://twitter.com/r0074g3n7/
buymeacoffee: https://www.buymeacoffee.com/error4004


👍
ReplyDelete